QMSR & ISO 13485: On 02-Feb-26, the FDA Final Rule comes into force. The amendments incorporate by reference (and so align more closely with) the international standard ISO 13485:2016, Medical Devices - Quality Management Systems - Requirements for regulatory purposes.
Did you know that cybersecurity is addressed in ISO 13485:2016, Clause 7.3?
Whether you are marketing a Medical Device Software (MDSW) product or a medical device where software drives or influences the device, you face cybersecurity issues.
In EU-regulated countries, the AI Act is a factor to consider; however, as it has been deferred to 2027, it is a topic for another day and is not considered here.
Here, we focus on cybersecurity threats rather than compliance.
Table of Contents (click to expand)
- Cybersecurity Threats in Medical Device Management
- Best Practices to Strengthen Medical Device Cybersecurity
- Risk Assessment
- Authentication and Access Control
- Data Encryption
- Software Updates and Patch Management
- Network Security
- Physical Security
- Security by Design
- Incident Response Plan
- Regulatory Compliance
- User Education
- Vendor Collaboration
- Continuous Monitoring
- Security Testing
- Legacy Device Management
- Patient Privacy
- Cyber Security and ISO 13485 Requirements
- Integrating Cybersecurity with Medical Device Management
- Managing and Providing Objective Evidence of Compliant Handling of Personal Data
- Protecting the Information Assets of Cloud-Based Apps
- Reassuring Stakeholders that Information Security is Taken Seriously
- Post-Market Surveillance and Regulatory Guidance
- Other Actions to Consider
Cybersecurity Attacks on Medical Devices
-
Cardiac Implants (Pacemakers/Defibrillators): Potential for battery drainage or unauthorized electrical shocks.
-
Insulin & Infusion Pumps: Vulnerable to remote dose manipulation or complete delivery stoppage.
-
Imaging Systems (MRI/CT/X-ray): Susceptible to malware that can alter images or diagnostic data.
-
Nurse Call Systems: Often cited as the highest-risk category due to unpatched software and weak security.
-
Legacy Systems: 53% of networked medical devices have at least one known critical vulnerability, often due to running unsupported operating systems such as Windows XP or Windows 7.
Best Practices to Strengthen Medical Device Cybersecurity
Medical devices, such as insulin pumps, pacemakers, infusion pumps, and diagnostic equipment, are increasingly connected to networks and the internet, exposing them to cyber threats. Ensuring the security of these devices is essential to protect patient safety, privacy, and the integrity of healthcare systems.
Here are some best practices for you to consider.
1. Risk Assessment: Manufacturers should conduct thorough risk assessments to identify potential vulnerabilities and threats in their devices. This includes considering how the device might be accessed or tampered with remotely.
2. Authentication and Access Control: Implement strong authentication mechanisms to ensure that only authorized personnel can access and configure the device. Use role-based access control to limit what different users can do.
3. Data Encryption: Ensure that data transmitted between the device and other systems is encrypted to protect patient information and prevent interception or tampering.
4. Software Updates and Patch Management: Keep the device's software up-to-date by regularly issuing patches and updates to address known vulnerabilities. Provide a mechanism for users to apply these updates easily.
5. Network Security: Medical devices should be designed to operate on secure networks. Use firewalls, intrusion detection systems, and other network security measures to protect against unauthorized access.
6. Physical Security: Physical access to the device should also be restricted. Prevent unauthorized users from physically tampering with or accessing the device.
7. Security by Design: Integrate security into the design and development of the device from the outset. Consider security throughout the product lifecycle, from concept to disposal.
8. Incident Response Plan: Develop and maintain an incident response plan to address cybersecurity breaches. This should include procedures for identifying, containing, and mitigating security incidents.
9. Regulatory Compliance: Ensure that your device complies with relevant regulatory standards and guidelines for cybersecurity in medical devices. In the United States, the FDA provides guidance on this topic.
10. User Education: Educate healthcare providers and end-users about the importance of cybersecurity and how to use the device securely. Promote best practices for password management and safe use.
11. Vendor Collaboration: Work with third-party vendors to ensure that any components or software used in your device meet security standards. Be aware of the supply chain security risks.
12. Continuous Monitoring: Continuously monitor the device and the network for signs of suspicious activity. Implement security monitoring and logging to detect and respond to potential threats.
13. Security Testing: Conduct regular security testing, including penetration testing and vulnerability assessments, to identify and address weaknesses in the device's security.
14. Legacy Device Management: For older devices that are no longer supported or updated, establish strategies to mitigate risks, such as network isolation or device replacement.
15. Patient Privacy: Safeguard patient privacy by ensuring that any data collected or transmitted by the device is handled in compliance with healthcare privacy laws (e.g., HIPAA in the United States).
Cyber Security and ISO 13485 Requirements
Clause 7.3 of ISO 13485:2016 includes the sub-clause 7.3.3, Design and development inputs, which states:
‘Inputs relating to product requirements shall be determined, and records maintained (see 4.2.5). These inputs shall include:
a) functional, performance, usability, and safety requirements, according to the intended use;
b) applicable regulatory requirements and standards;
c) applicable output(s) of risk management;
d) as appropriate, information derived from previous similar designs;
e) other requirements essential for the design and development of the product and processes.
These inputs shall be reviewed for adequacy and approved.
Requirements shall be complete, unambiguous, able to be verified or validated, and not in conflict with each other.’
You can be certain that your Certification Body (or Notified Body in the EU) will interpret ‘c) applicable output(s) of risk management’ as requiring that cybersecurity aspects be addressed where your device transmits, receives, and/or stores data.
Integrating Cybersecurity with Medical Device Management
Cybersecurity is an integral part of our ISO 13485 training courses, recognizing that, in medical devices, it is an ongoing process that requires collaboration among manufacturers, healthcare providers, regulatory agencies, and cybersecurity experts to ensure patient and healthcare system safety and security. As technology evolves, so should medical device security measures to stay ahead of emerging threats.
Let’s look at examples of how cybersecurity supports medical device management.
1. Managing and providing objective evidence of compliant handling of Personal Data
Manufacturers are being asked to demonstrate compliance with a wide range of regulatory and sector-specific requirements for patient data security. The list includes...
- EU GDPR
- UK GDPR
- UK DPA 2018
- UK PECR (Privacy and Electronic Communications Regulations)
- CPPA (California)
- CPRA (California)
- UK NHS Digital Technology Assessment Criteria (DTAC)
- SOC 2 compliance
- ISO 27701
- ISO 27018
- ISO 27799
- US Health Insurance Portability and Accountability Act (HIPAA)
- And so on.
Demonstrating compliance on an individual basis would be a daunting task; it is far better to address all information security under an ISMS certified to ISO 27001. The independent annual audits will provide ongoing evidence of compliance with all applicable requirements.
An added bonus: you limit the number of external audits required.
2. Protecting the information assets of cloud-based apps
These can be standalone apps or apps that save and/or sync data with a smartphone, smartwatch, or similar device. Frequently, questions arise about whether end-to-end encryption is provided for transmitted data. The obvious answer is to implement ISO 27001, with independent auditing confirming ongoing compliance with regulatory and contractual requirements.
3. Reassuring stakeholders that information security is taken seriously.
Stakeholders, including major customers, hospitals, health services, and others, have cybersecurity concerns. And this in addition to concern about protecting personal information and customer/supplier intellectual property. There are two concerns here...
- Is cybersecurity sufficiently robust to minimize the chances of a ransom attack leading to interruption to the provision of products and/or services (e.g., maintenance of medical devices)?
- Is cybersecurity sufficiently robust to prevent a successful attack on the stakeholders' computer network arising from a breach of your cybersecurity?
In both cases, ISO 27001 certification can provide the reassurance that's needed.
Post-market Surveillance and Regulatory Guidance
Regulatory Authorities globally are now keenly aware of the havoc that cybercriminals could cause and the near certainty that they will do so. At the very minimum, your future Post-Market Surveillance must include cybersecurity and the protection of information relating to devices and the persons using them, in addition to patient data. The topic and associated threats are vast, and Regulators are struggling to prepare and issue official Guidance. In the meantime, you must address the issue by ensuring that data protection is part of your Medical Device Risk Management system.
Other Actions to Consider
While compliance with its requirements would likely be ‘overkill’ in many instances, we would recommend that you examine ISO 27001, the information security standard (and the companion standard, ISO 27002), for ideas on the types of controls that should be in place to protect both your product and the end-user/patient.
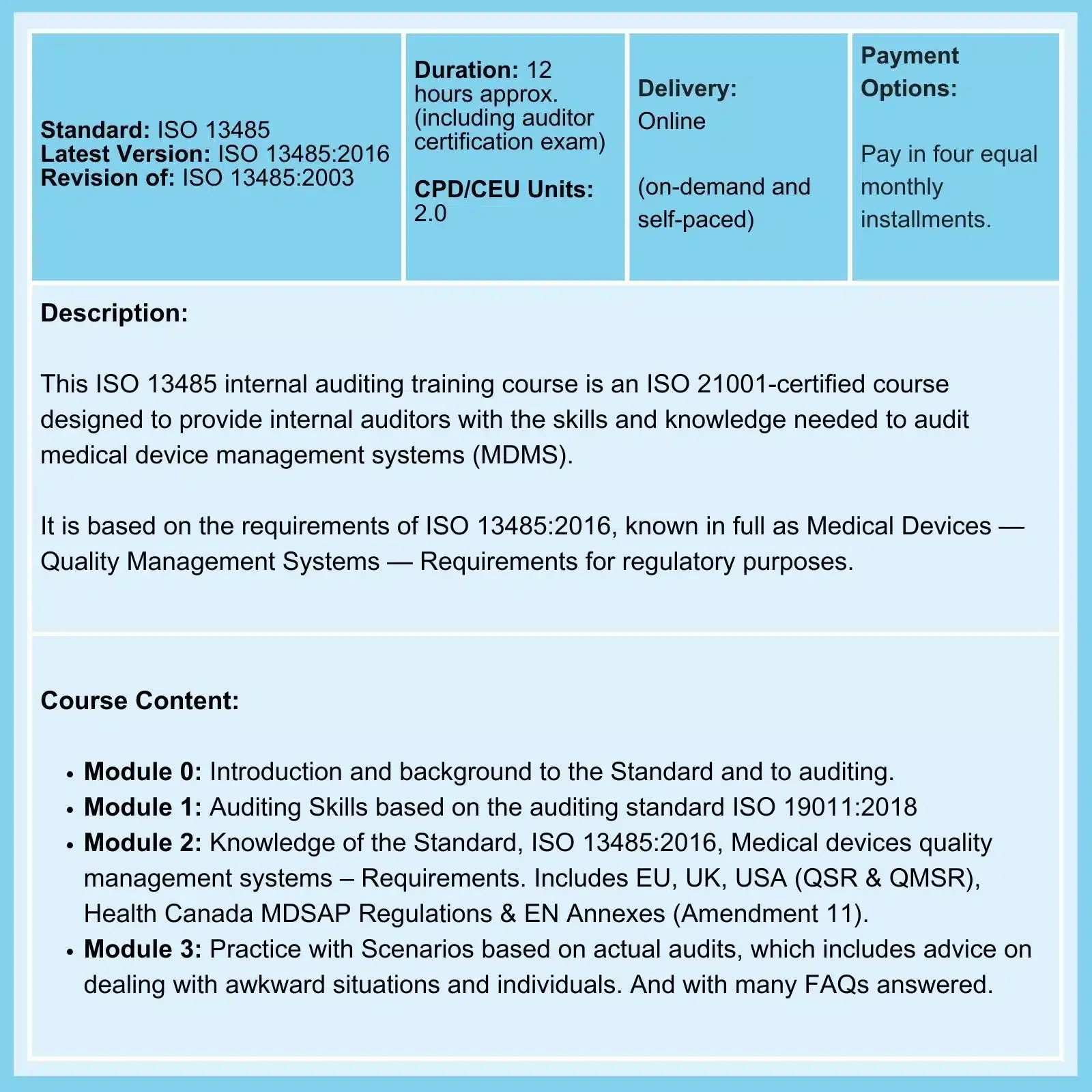
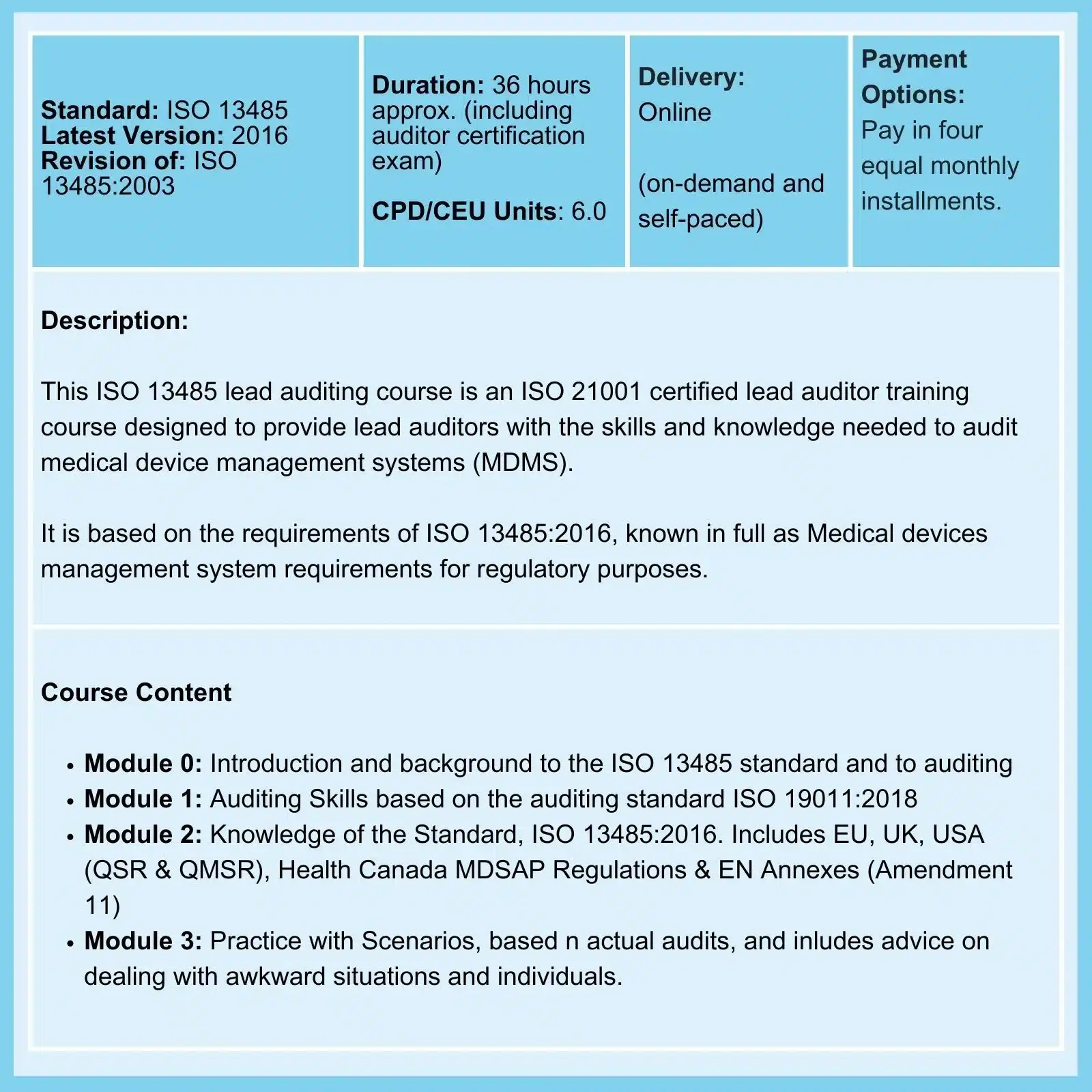
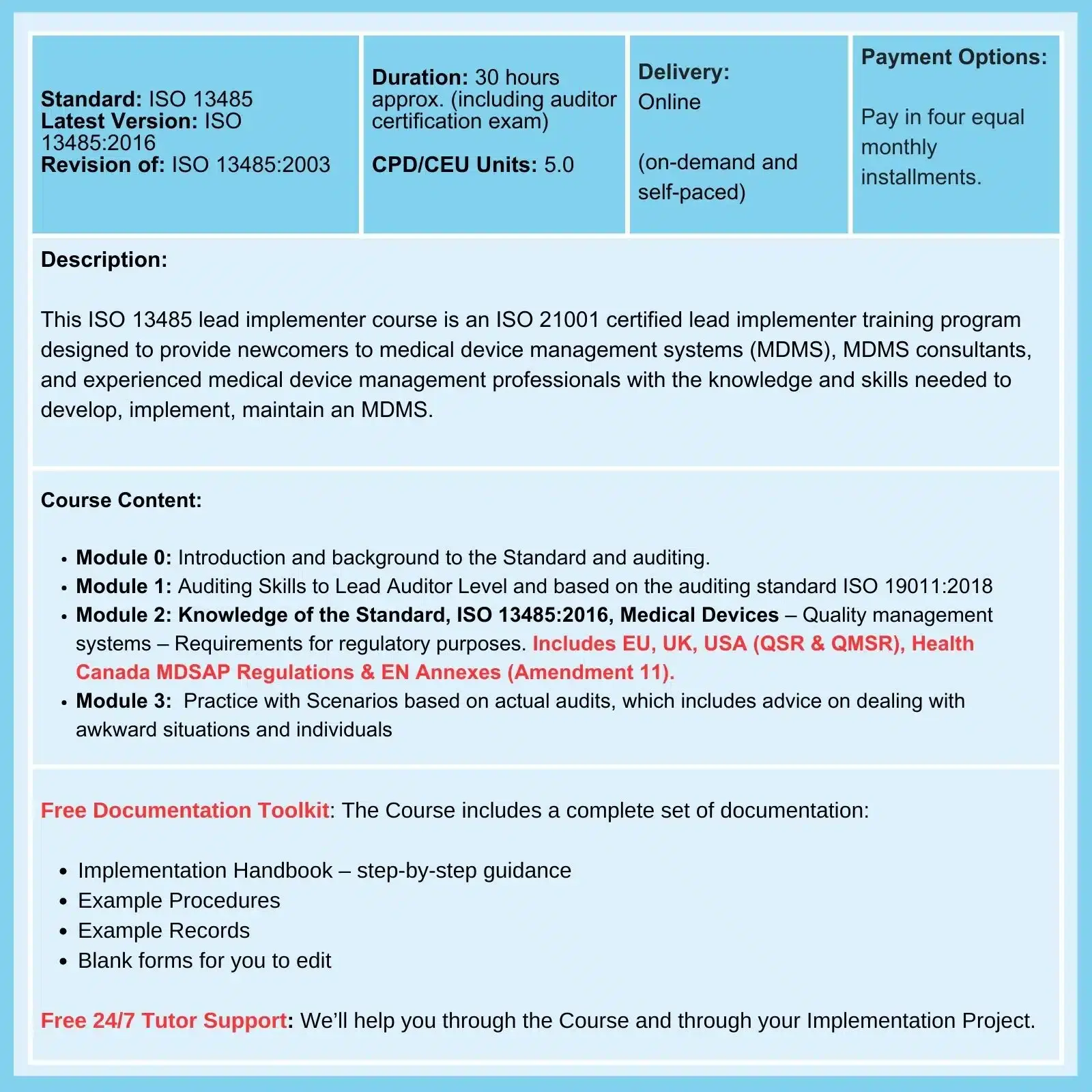
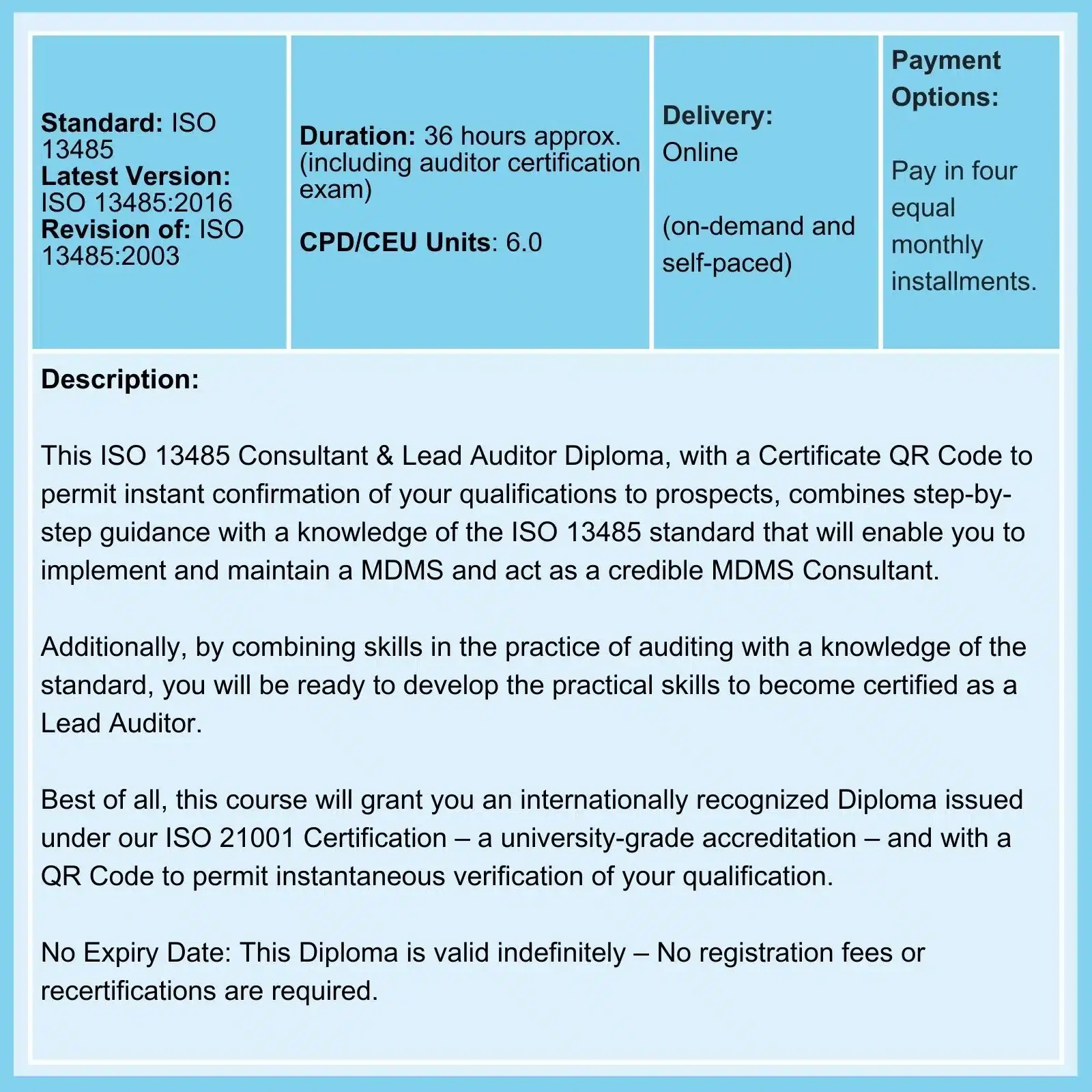
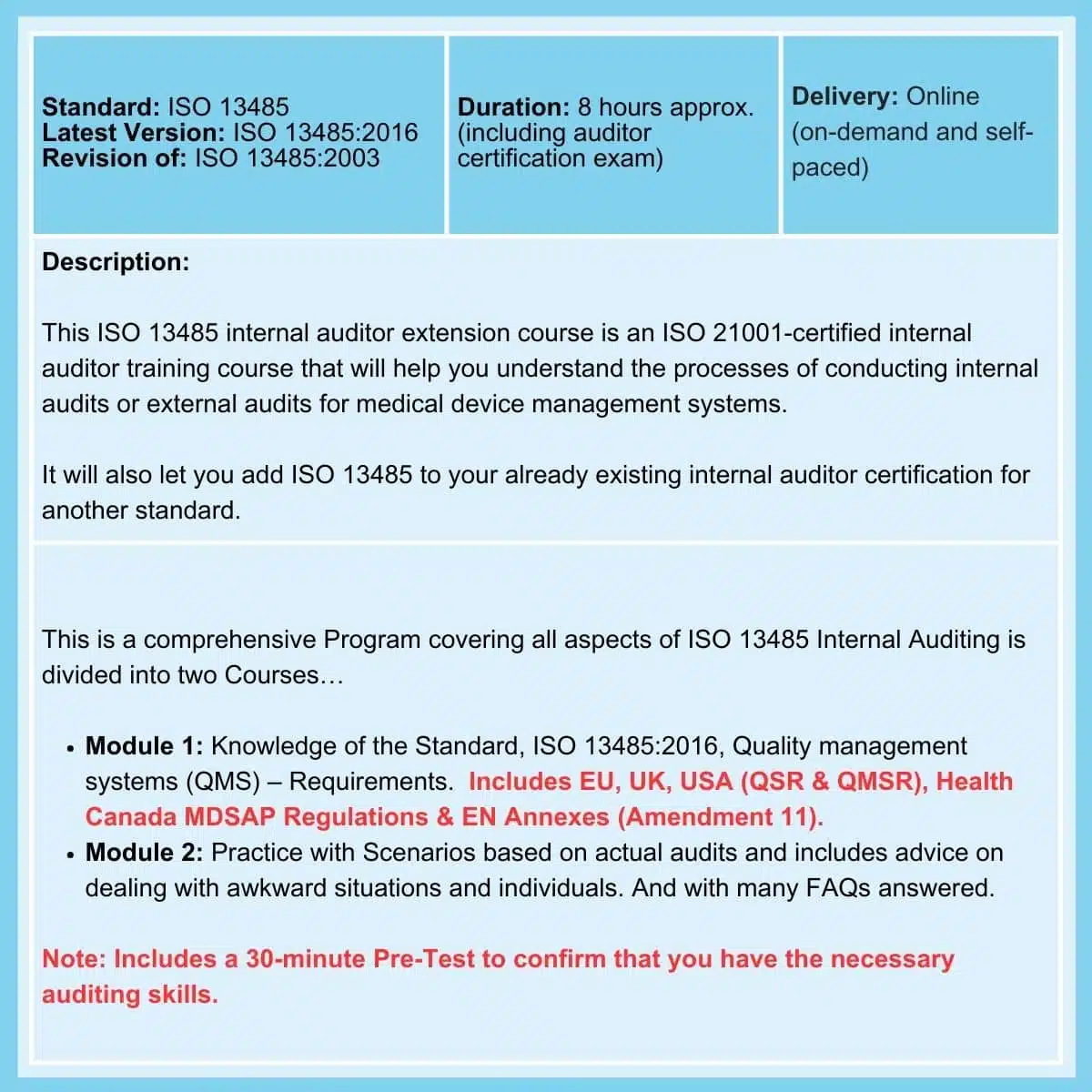
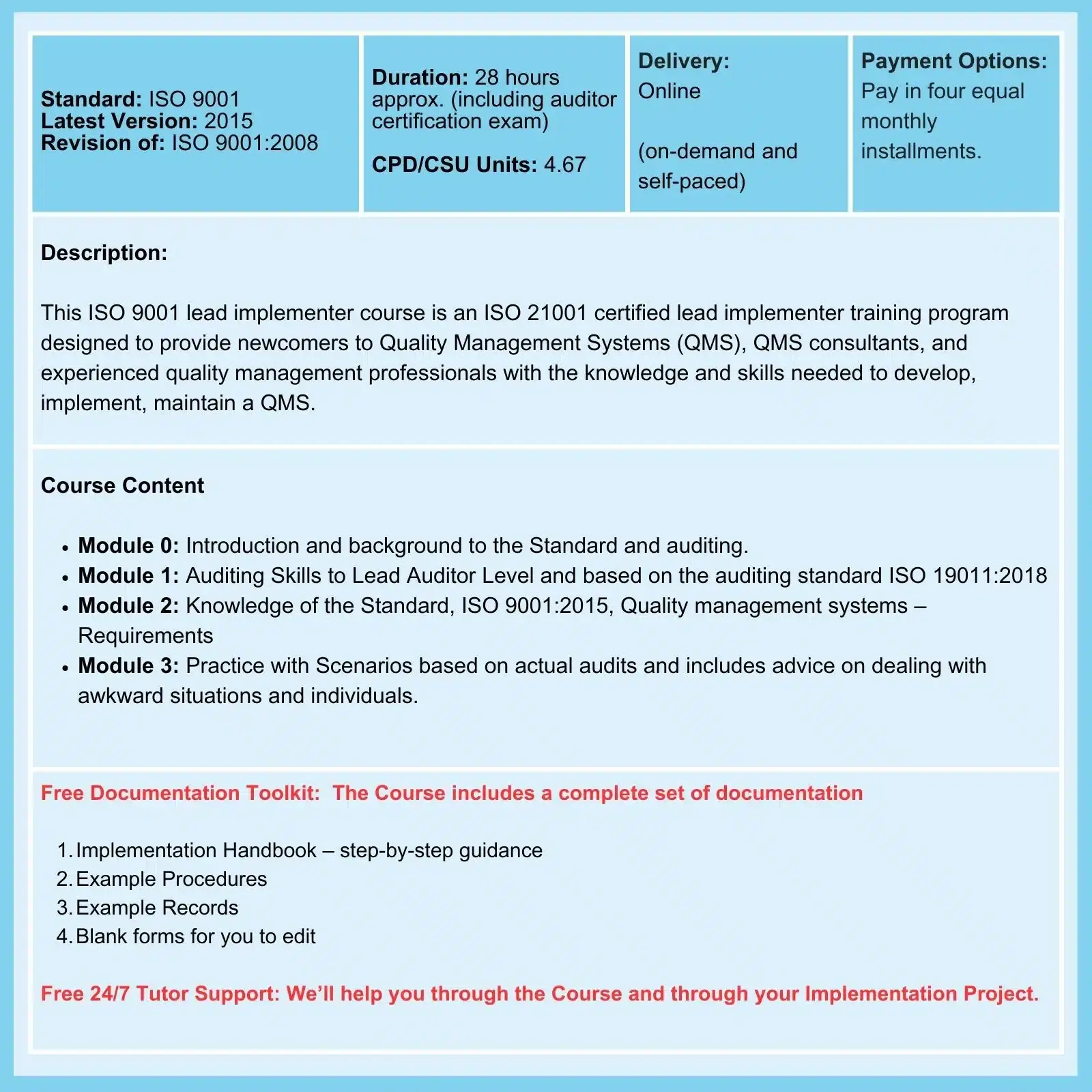
Related Courses
deGRANDSON Global is an ISO Certified Educational Organization
In October 2024, we secured ongoing certification to three education-related ISO Standards. We now have a university-grade management system in place that conforms to the requirements of …
We have chosen ISO 21001 certification because, unlike IRCA and Exemplar badges (which, in our opinion, are commercially compromised), it is based on independent third-party assessment. It is a ‘university grade’ standard in use globally by schools, colleges, and universities to demonstrate their competence.
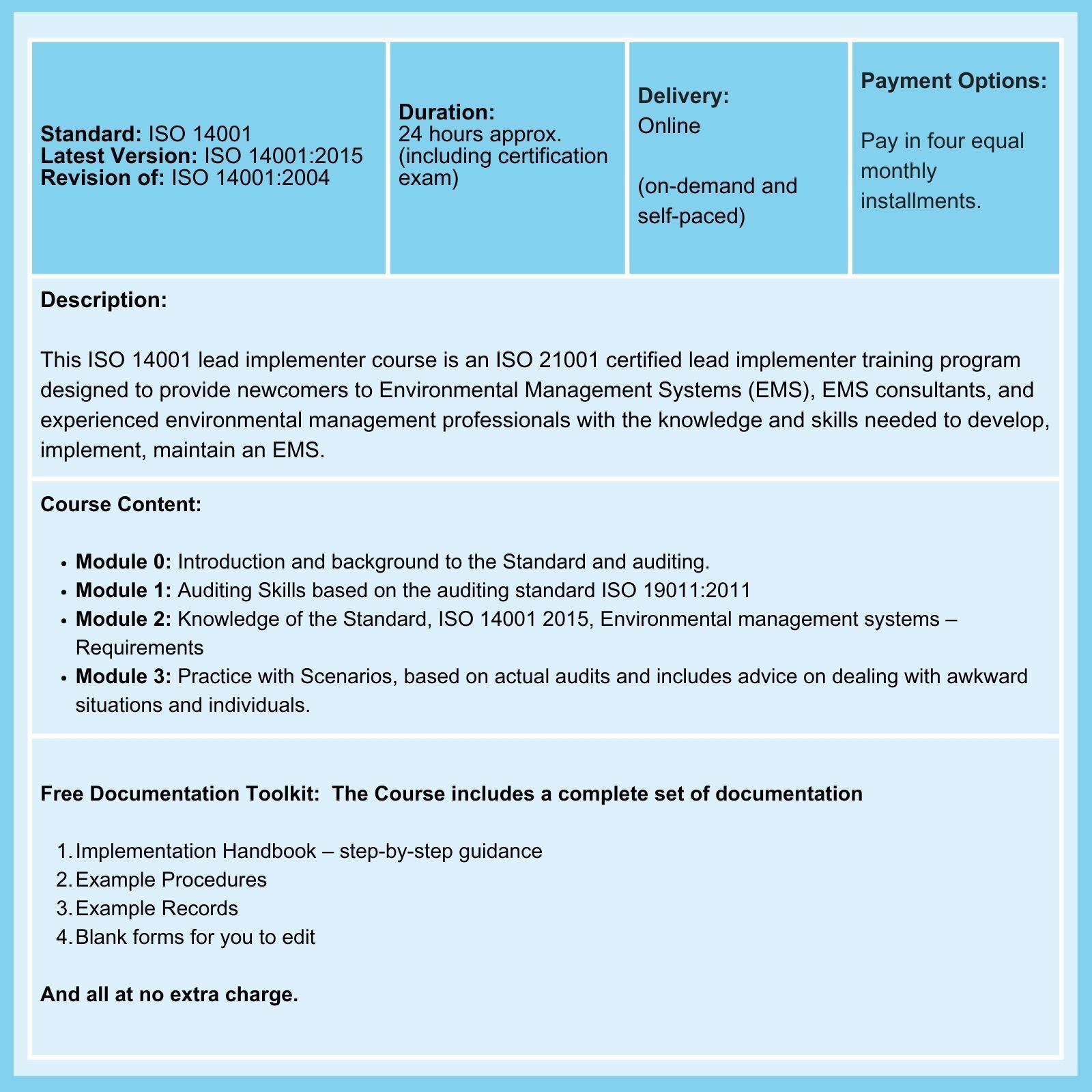
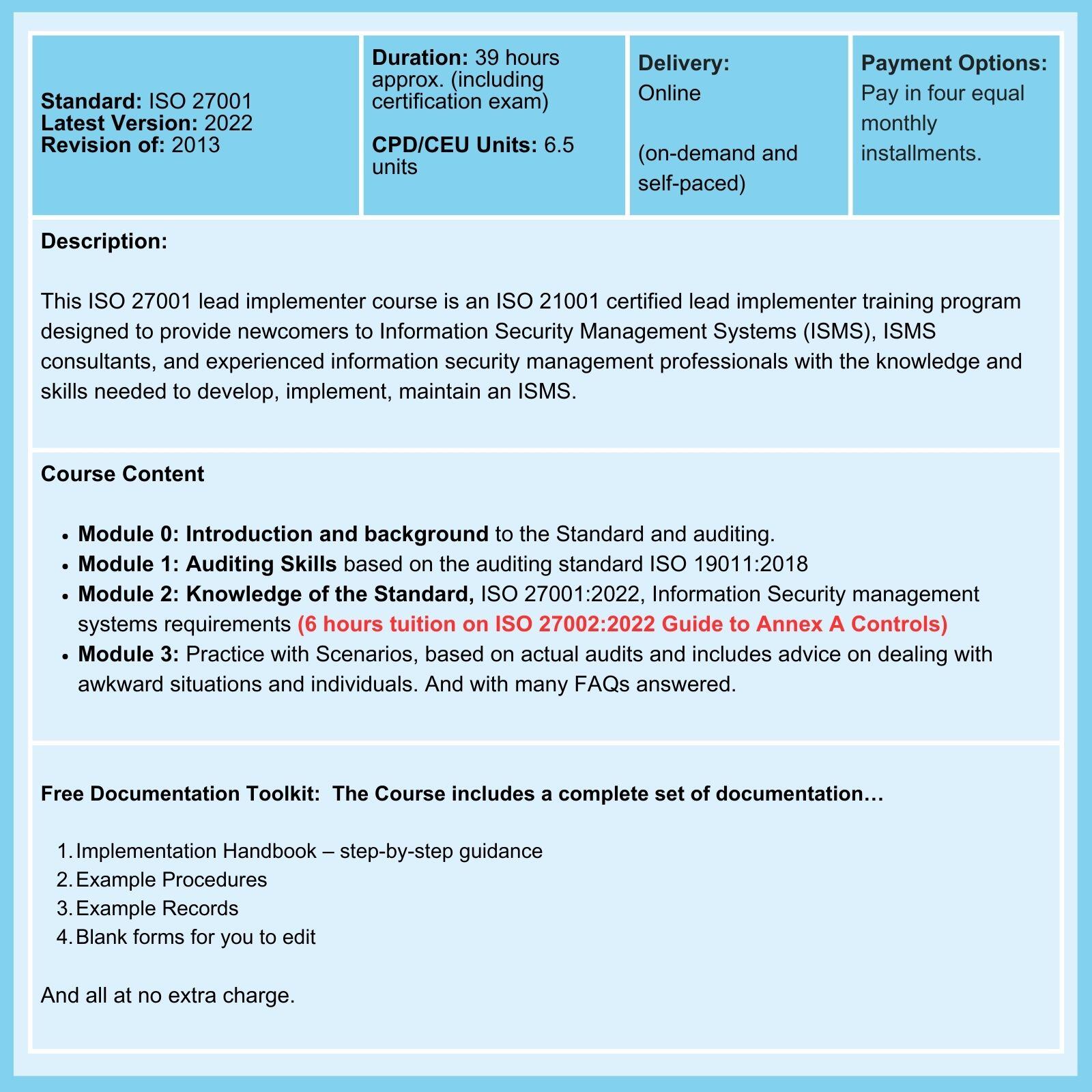
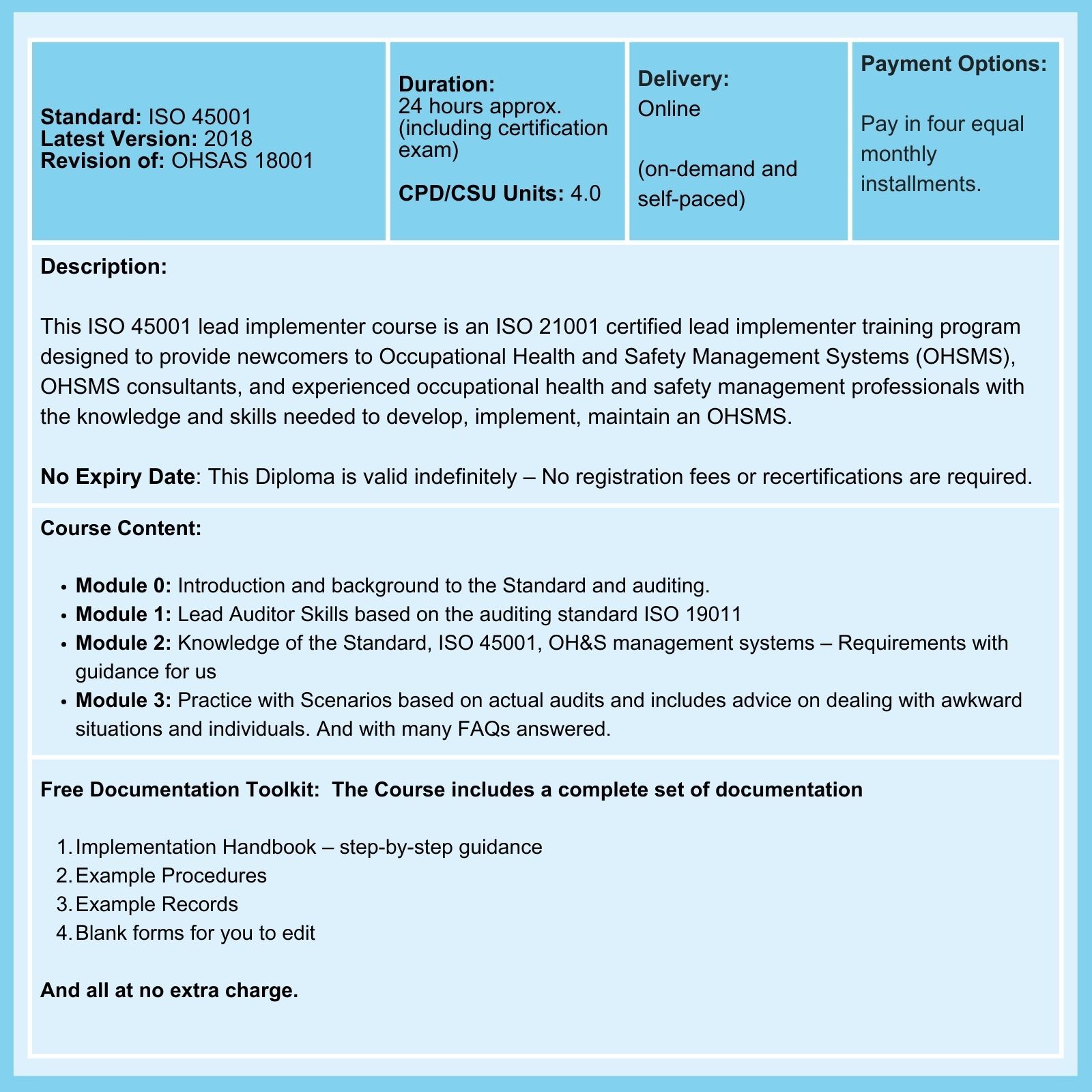
We offer courses for ISO 9001, ISO 13485, ISO 14001, ISO 17025, ISO 27001, ISO 45001, Data Protection, and Risk Management, among others.